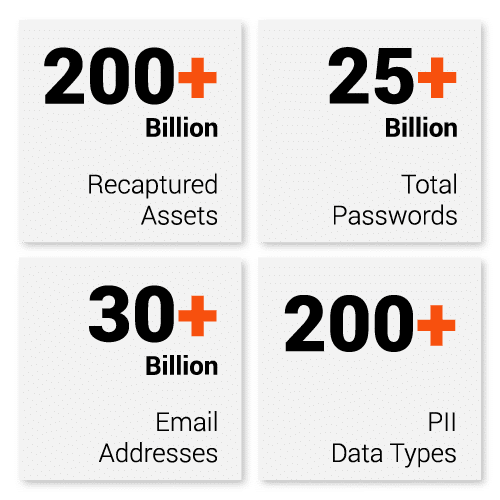
Protect your enterprise and your customers with account takeover and fraud prevention solutions backed by the largest and most up-to-date collection of recaptured data from breaches, malware-infected devices, and other underground sources. Cybersecurity and Backup
RADSPY Data Protection
Our Licence Options
Prevent compromised data putting your business at risk!
SMB Small ATO Prevention
- Access to a secured portal for managing watchlists and reviewing reported data
- Watchlist capacities of 2 domains and 25 personal email
addresses - Real-time email alerts
- Infected user reports, showing devices discovered to be infected with malware
SMB Medium ATO Prevention
- Access to a secured portal for managing watchlists and reviewing reported data
- Watchlist capacities of 5 domains and 100 personal email addresses
- Real-time email alerts
- Infected user reports, showing devices discovered to be infected with malware
SMB Large ATO Prevention
- Access to a secured portal for managing watchlists and reviewing reported data
- Watchlist capacities of 10 domains and 200 personal email addresses
- Real-time email alerts
- Infected user reports, showing devices discovered to be infected with malware
Enterprise Employee ATO Prevention:
- Access to a secured portal for managing watchlists and reviewing reported data
- Watchlist capacities of 20 domains and 1,000 personal email addresses, and 20 egress IP addresses
- Use of RADSPY’s Enterprise API
- Real-time email alerts
- lnfected user reports, showing devices discovered to be infected with malware
Large Enterprise Employee ATO Prevention
- Access to a secured portal for managing watchlists and reviewing reported data
- Watch list capacities of SO domains and 3,000 personal email addresses, and SO egress IP addresses
- Use of RADSPY’s Enterprise API
- Real-time email alerts
- Infected user reports, showing devices discovered to be infected with malware
Global Enterprise Employee ATO Prevention
- Access to a secured portal for managing watch lists and reviewing reported data
- Watchlist capacities of 100 domains and 10,000 personal email addresses, and 100 egress IP addresses
- Use of RADSPY’s Enterprise API
- Real-time email alerts
- Infected user reports, showing devices discovered to be infected with malware
PRICING
| Package | Description | Commit Period | Annual Fee | Monthly Fee (Annual Commit) | Per mailbox | Domains |
| Entry Level | 1 to 2 scans a month with limited results to 50 email accounts | Monthly | NA | $125.00 | $2.70 | 1 |
| SMB Small | Employee ATO Preevention, SMB 1-99 email accounts | 1 Year | $2,495.00 | $229.00 | $2.31 | 2 |
| SMB Medium | Employee ATO Preevention, SMB 100-249 email accounts | 1 Year | $5,795.00 | $539.00 | $2.13 | up to 5 |
| SMB Large | Employee ATO Preevention, SMB 250-500 email accounts | 1 Year | $10,795.00 | $989.00 | $1.98 | up to 10 |
| Enterprise 1 | Employee ATO Preevention, SMB 501-100 email accounts | 1 Year | $16,595.00 | $1,529.00 | $0.89 | up to 20 |
| Enterprise 2 | Employee ATO Preevention, SMB 1001-1700 email accounts | 1 Year | $23,495.00 | $2,159.00 | $1.27 | up to 20 |
| Enterprise 3 | Employee ATO Preevention, SMB 1701-2500 email accounts | 1 Year | $33,195.00 | $3,049.00 | $1.22 | up to 20 |
| Large Enterprise 1 | Employee ATO Preevention, SMB 2501-5000 email accounts | 1 Year | $44,195.00 | $4,059.00 | $0.81 | up to 50 |
| Large Enterprise 2 | Employee ATO Preevention, SMB 5001-7500 email accounts | 1 Year | $55,195.00 | $5,059.00 | $0.67 | up to 50 |
| Large Enterprise 3 | Employee ATO Preevention, SMB 7501-10000 email accounts | 1 Year | $66,295.00 | $6,079.00 | $0.61 | up to 50 |
| Global Enterprise 1 | Employee ATO Preevention, SMB 10001-20000 email accounts | 1 Year | $99,395.00 | $9,119.00 | $0.46 | up to 100 |
| Global Enterprise 2 | Employee ATO Preevention, SMB 20000-40000 email accounts | 1 Year | $149,095.00 | $13,669.00 | $0.34 | up to 100 |
| Global Enterprise 3 | Employee ATO Preevention, SMB 40001-80000 email accounts | 1 Year | $206,995.00 | $18,979.00 | $0.24 | up to 100 |
| Global Enterprise 4 | Employee ATO Preevention, SMB 80000-150000 email accounts | 1 Year | $275,995.00 | $25,299.00 | $0.17 | up to 100 |
FEATURES
A New & Better Way to Protect Your Enterprise
The Largest Collection of Recaptured Data
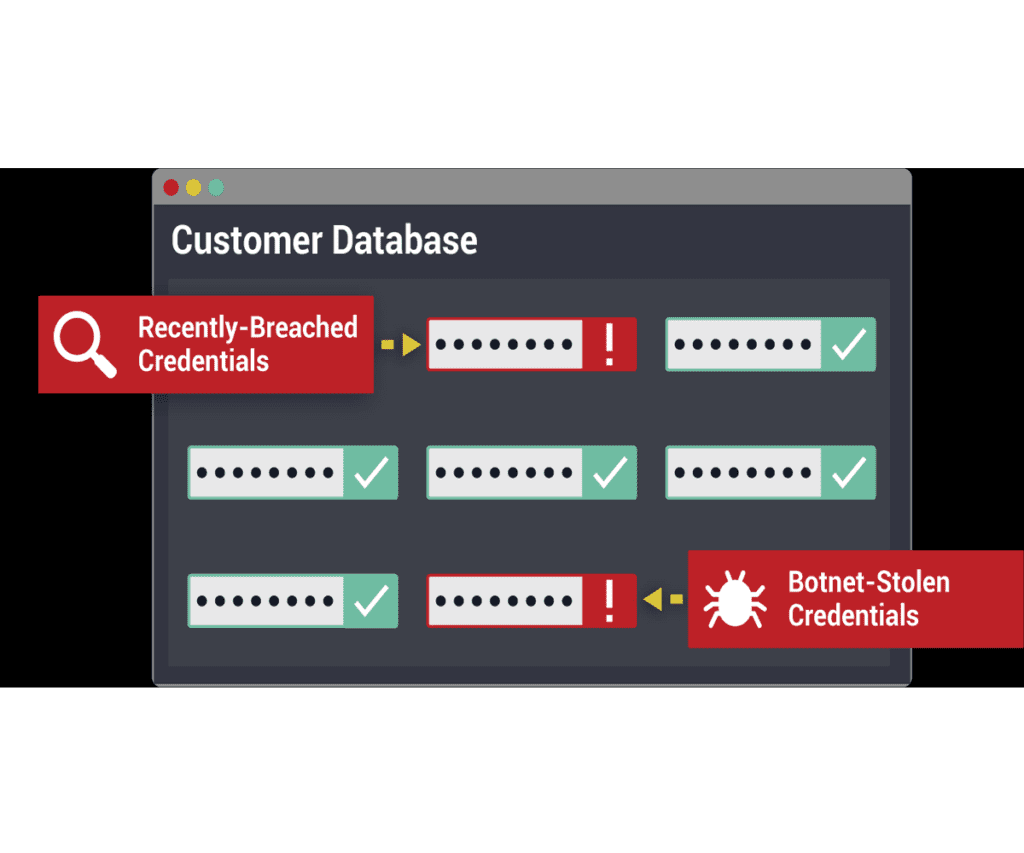
Insights from Botnet Logs
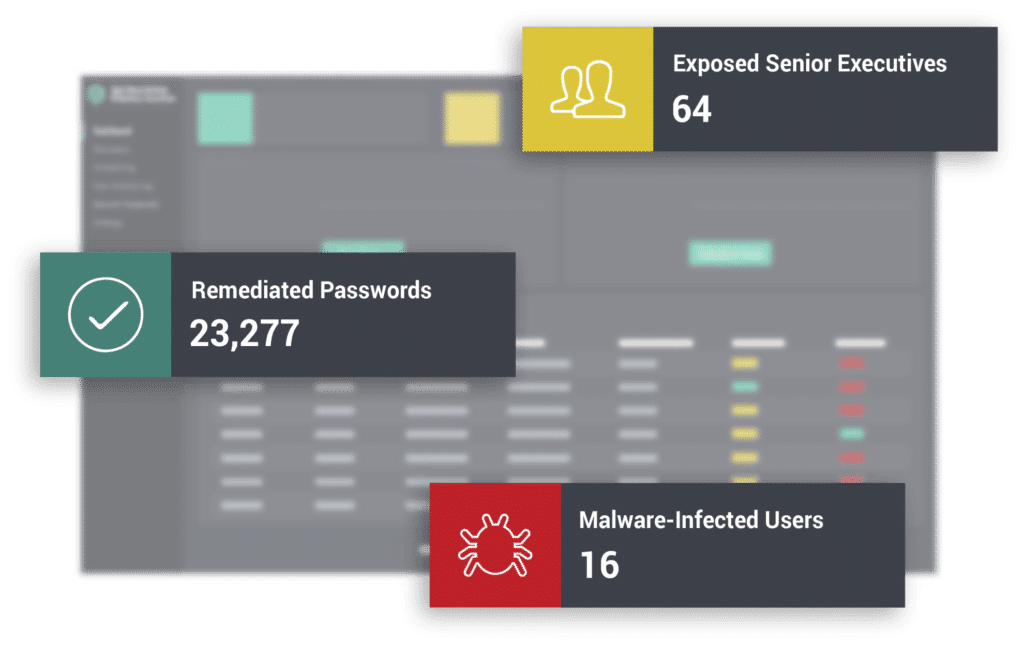
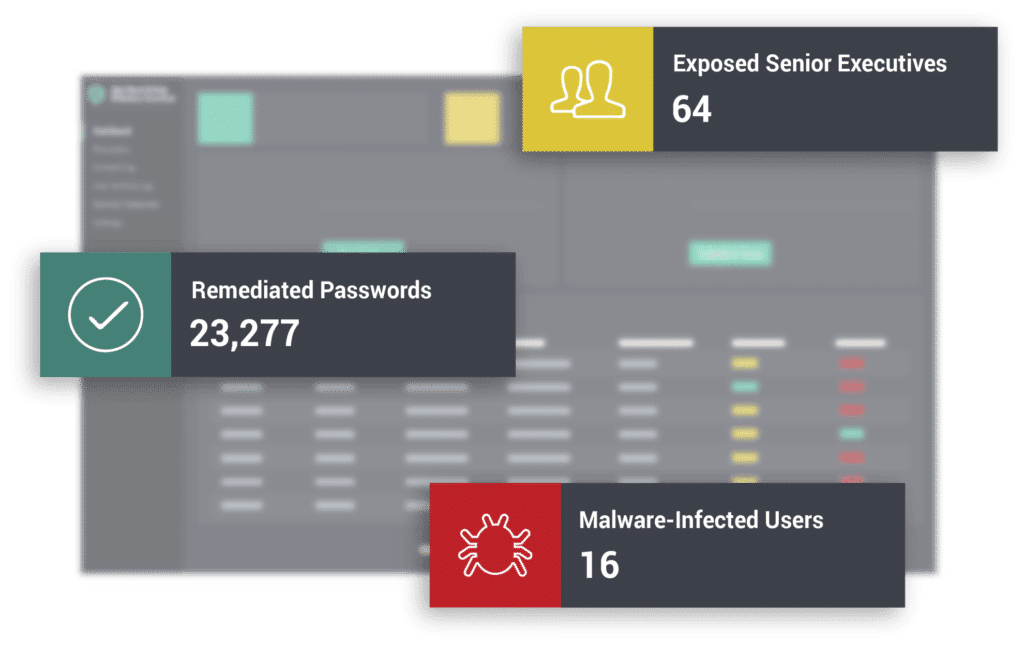
Identify employees whose corporate or personal devices are infected with malware, meaning their credentials and potentially sensitive company information is exposed to criminals. These high-severity exposures are flagged by RADSPY for immediate remediation.
Employee ATO Prevention
Employee account takeover is a type of online fraud that occurs when attackers use stolen logins to gain access to corporate accounts. When employees reuse passwords across multiple online accounts, criminals can exploit credentials that have been exposed in third-party data breaches to access their corporate accounts.
RADSPY Employee Account Takeover Prevention enables enterprises to stay ahead of account takeover and targeted attacks like ransomware by detecting and resetting compromised passwords early, before criminals have a chance to use them.


VIP Protection
Employee account takeover can result in substantial losses for enterprises. Senior executives, board members, and employees with privileged access are all at especially high risk of being targeted, and attackers may use creative methods to infiltrate their accounts. While corporate logins can be protected by enterprise security teams, executives’ personal accounts fall outside of corporate control. If an executive’s personal password is exposed in a data breach, their unprotected accounts may provide entry points for a motivated attacker to access corporate resources.
RADSPY VIP Guardian helps you extend your employee account takeover prevention strategy to key executives’ personal accounts for an added layer of protection, without invading their privacy. With RADSPY, you can give executives access to their own breach data and empower them to protect their vulnerable accounts.
Active Directory Guardian

Get Rich Insights From Recaptured Data
Automatically Overcome Password Reuse
A New Way to Protect Your Customers & Your Bottom Line
What Makes RADSPY Different?
With recaptured data you can reduce fraud losses for your business and protect your customers from account takeover so they keep coming back again and again.
Protect Your Customers From Account Takeover Fraud
Account takeover is a common form of fraud in which criminals use stolen credentials to gain illegitimate access to a victim’s accounts, often using credentials that have been exposed in previous data breaches. When your consumers reuse passwords, they become easy targets for cybercriminals.
With RADSPY Consumer Account Takeover Prevention, you can detect and remediate stolen passwords before bad actors have a chance to use them. RADSPY checks your consumer credentials against the largest repository of recaptured data in the world (data from third-party breaches, malware-infected devices, and other underground sources) and alerts you to exposures that could put your consumers at risk.
Using the RADSPY API, you can easily integrate RADSPY data into your existing workflows and applications, including common SIEMs and TIPs. The API provides high-volume access to the RADSPY dataset to help you detect matches, reset exposed credentials, and support your overall consumer account takeover prevention strategy.

Make faster, more accurate fraud decisions using recaptured data from criminal communities.
Overcome Poor Consumer Password Hygiene

The Missing Piece of Your Fraud Prevention Framework
Stop the Hardest-to-Detect Fraud
Transform Your Investigations

Fight Financial Fraud
Stop Human Trafficking
Investigate Retail Cyber Fraud
Investigate Criminals Harming Your Business
Use Criminals’ Data Against Them
Understand How You Can Accelerate Investigations with Radspy
Draw on RADSPY's Rich Dataset and Maltego Tansforms to Help Your Team
Maltego Transforms
Data Partnerships with RADSPY